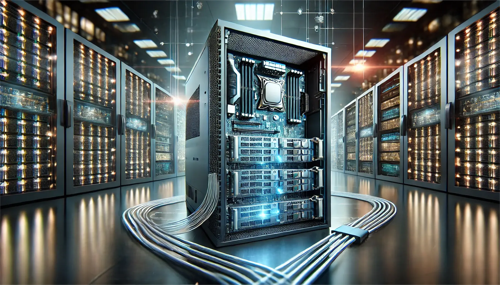
when connecting overseas business or circumventing domestic filing requirements, rapid deployment of u.s. filing-free high-defense servers is a common choice. this article sorts out the process of getting started with the u.s. registration-free high-defense servers from a professional perspective, helping you to efficiently complete the selection, configuration and launch, ensuring both performance and security.
before purchasing, evaluate the supplier's qualifications, network backhaul and computer room location, ddos protection capabilities, and after-sales response. give priority to computer rooms with multi-line bgp or single-line high-quality backhaul, and confirm that the protection level and bandwidth can be increased as needed.
the location of the computer room affects access delay and stability. focus on the east coast or west coast nodes for target users, and also consider the operator's interconnection conditions. properly plan public network ip, intranet isolation and routing strategies to facilitate subsequent expansion and traffic management.
select a combination of cpu, memory, disk, and network bandwidth based on the type of business. web, applications and databases can be deployed in layers. linux distributions or windows are commonly used as operating systems, and systems with mature mirroring and security hardening solutions are preferred.
enable the ddos high-defense service provided by the operator or supplier, and set cleaning thresholds and policy templates. preset protection rules for common attack types, combined with traffic alarm thresholds, to ensure that cleaning nodes take effect in a timely manner and avoid accidental killing of normal traffic.
deploy host firewalls and cloud firewalls at the system and network layers respectively, minimize open ports, and use whitelists to manage ssh/rdp access. use security groups or acls to limit mutual access to internal services and reduce the horizontal attack surface.
caching static content in combination with cdn can reduce the pressure on the origin site and reduce bandwidth costs; the application layer uses load balancing to achieve traffic distribution and failover. configure health check and session persistence to ensure smooth switching and sensitive detection.
after completing system updates, necessary software installation and performance tuning, deploy web services, databases and middleware. enable log collection and centralized management, sort out dependencies, and write repeatable deployment scripts or container images.
use reliable dns services to implement authoritative resolution and fast switching strategies, and record ttl settings to facilitate emergency switching. deploy ssl/tls certificates for domain names, configure automatic renewal and https forced redirection, and improve transmission security.
establish key indicator monitoring (bandwidth, latency, cpu, memory, number of connections, etc.) and configure multi-level alarms. design regular backup and failure recovery drills to ensure rapid restoration of service and data integrity in the event of an attack or failure.
before going online, perform traffic pressure testing, regression testing and security scanning, and use phased grayscale releases to observe real traffic performance. connect the emergency plan and verify the switching process to ensure that the protection and fallback mechanism are effective under abnormal traffic.
summary of recommendations: when deploying u.s. registration-free high-defense servers, model selection, network design, and security strategies should be coordinated, and attention should be paid to observability and emergency plans. implement configuration, testing and drills step by step, and maintain continuous optimization of protection rules and monitoring alarms to achieve stable and safe overseas service delivery.

- Latest articles
- Japanese Native Ip L2tp Architecture Design And Access Control Suggestions In Enterprise Scenarios
- How To Set Up Security Protection And Monitoring After Purchasing The American Station Group Server
- How Does An Enterprise Choose And Configure A High-defense Us Free Virtual Server To Ensure Stable Access?
- Temporary Solution For Thai Card Phone Showing Serverless Using Wifi With Hotspot Alternative
- Compliance And Security Perspective Assessing U.s. Data Protection Practices Of Largest Cloud Servers
- Legal Compliance And Data Sovereignty Are Surging. Compliance Issues That Vietnam Must Pay Attention To When Looking For Servers
- Traffic Dispersion And Bandwidth Management Teach You How To Rationally Allocate Resources In A Cloud Cluster Korean Server Environment.
- Practical Ways To Save Money And Reduce Budget Pressure
- Security Strategies And Traffic Cleaning Methods When Deploying Taiwan’s Native Ip Odin
- Emergency Plan: Switching And Traffic Diversion Methods During Hong Kong High Defense Server Rental Attack
- Popular tags
-
Analysis Of The Potential Consequences And Impact Of The Shutdown Of Root Servers In The United States
this article provides an in-depth analysis of the potential consequences and impacts of the shutdown of root servers in the united states, including the impact on internet stability, security, and global network structure. -
Cost-effectiveness Analysis And Purchasing Suggestions For American High-defense Servers
this article analyzes the cost-effectiveness of high-defense servers in the united states and provides purchasing suggestions to help users choose the appropriate server. -
The Latest Perfect International Server Leopard Mount Redemption Method And Event Instructions
this article details the latest perfect international server leopard mount redemption method and activity instructions, including participation conditions, redemption process, precautions and practical tips to help players obtain mounts efficiently.